Ijraset Journal For Research in Applied Science and Engineering Technology
- Home / Ijraset
- On This Page
- Abstract
- Introduction
- Conclusion
- References
- Copyright
Comprehensive Approaches for Detecting and Mitigating Distributed Denial of Service (DDoS) Attacks in Modern Network Environments
Authors: Syed Ali Nawaz Zaidi, Jianping Li, Yubo Tan
DOI Link: https://doi.org/10.22214/ijraset.2025.66669
Certificate: View Certificate
Abstract
Distributed Denial of Service (DDoS) attacks remain one of the most significant threats to the security and availability of online services. These attacks exploit multiple systems, typically compromised devices, to flood a target server with excessive traffic, causing service disruption and resource depletion. Over the years, DDoS attacks have evolved in both scale and complexity, posing new challenges to cybersecurity professionals. This paper provides an in-depth analysis of DDoS attacks, categorizing various types, exploring their impact on both businesses and infrastructure, and reviewing the latest detection and mitigation techniques. We focus on the intersection of machine learning, network traffic analysis, and cloud-based solutions as advanced strategies to counteract these persistent threats. Additionally, we explore case studies highlighting the real-world applications of these methods. The paper concludes by proposing future research directions and the role of emerging technologies such as AI and blockchain in strengthening DDoS defenses.
Introduction
I. INTRODUCTION
Distributed Denial of Service (DDoS) attacks have been one of the most prevalent forms of cyberattacks targeting organizations and infrastructure across the globe. These attacks aim to overwhelm online systems with malicious traffic, often causing severe disruptions to services such as e-commerce, financial platforms, and critical government operations. Over time, DDoS attacks have grown in both sophistication and scale, challenging traditional methods of detection and mitigation. This paper aims to provide a comprehensive review of DDoS attacks, focusing on current techniques for detecting and mitigating these threats while evaluating the latest innovations in the field.
II. UNDERSTANDING DDOS ATTACKS
A. Definition and Mechanism
A DDoS attack is a cyberattack in which multiple systems (often a botnet) are used to target a single server, website, or network infrastructure. These systems are often compromised devices like computers, IoT devices, and even routers. The attackers control these systems remotely, instructing them to send massive amounts of data to the target, exhausting its resources such as CPU power, memory, and bandwidth. The goal is to make the target system either slow to a halt or completely unavailable.
B. Types of DDoS Attacks
1) Volumetric Attacks: These attacks involve overwhelming the target with massive amounts of traffic. Common examples include UDP floods and ICMP floods.
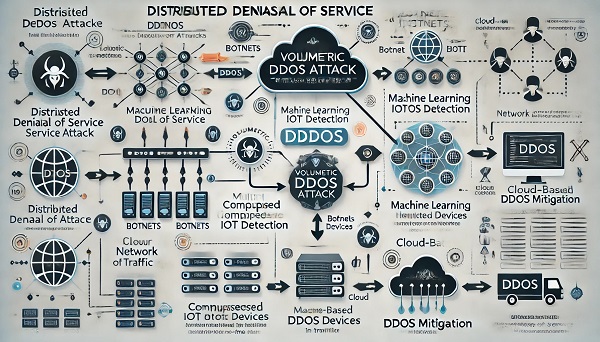
Fig. 1 volumetric attacks
Here is a diagram illustrating the detection and mitigation strategies for DDoS attacks, including volumetric attack flow, machine learning-based detection, and cloud-based mitigation methods. This diagram illustrates how volumetric attacks work, with botnets (compromised IoT devices) sending massive amounts of traffic to overwhelm a target server, which is the basis for volumetric DDoS attacks (e.g., UDP floods, ICMP floods).
- Protocol Attacks: These attacks exploit weaknesses in networking protocols. A SYN flood, for example, is a TCP-based attack that consumes server resources.
- Application Layer Attacks: These attacks target specific applications such as HTTP or DNS servers, often with relatively low traffic but highly malicious requests. For example, HTTP floods overwhelm web servers by sending numerous seemingly legitimate HTTP requests.
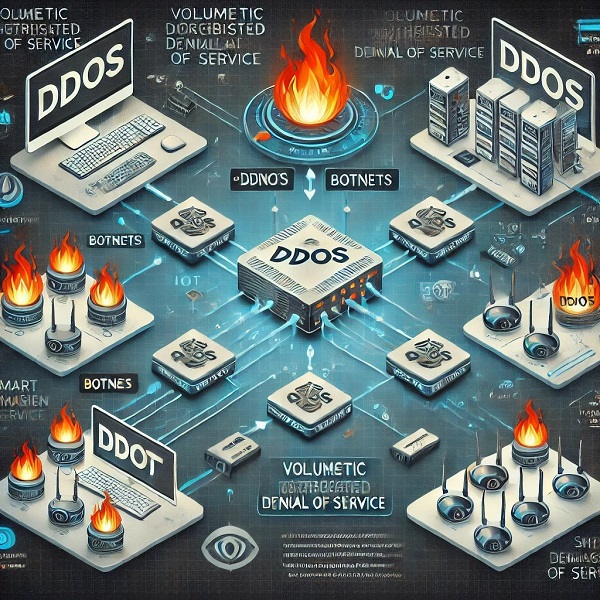
Fig. 2 Volumetric DDoS Attack Flow
Here is a diagram illustrating the flow of a volumetric DDoS attack, where multiple compromised IoT devices overwhelm a target server with traffic. This diagram showcases how machine learning algorithms analyze network traffic, identifying anomalies in real-time to detect DDoS attacks. It demonstrates the modern approach of using AI for proactive detection and mitigation of evolving DDoS threats.
C. Evolution and Trends
Initially, DDoS attacks were relatively simple, involving basic flooding techniques. However, modern DDoS attacks are more complex and include distributed botnets and reflection/amplification attacks, where attackers use vulnerable servers to magnify the traffic volume sent to the target.
III. THE IMPACT OF DDOS ATTACKS
A. Financial Losses
The direct financial impact of DDoS attacks can be severe. According to a report by the Ponemon Institute, the average cost of a DDoS attack for an organization can exceed $2 million when considering lost business, customer churn, and the need for IT remediation.
B. Reputational Damage
Extended downtime caused by DDoS attacks can significantly damage a company's reputation. Customers, especially in the e-commerce and financial sectors, may lose confidence in the availability and security of services provided by organizations under attack.
C. Infrastructure Strain
DDoS attacks can strain an organization’s IT infrastructure, leading to the overuse of network bandwidth and server resources. This not only disrupts normal operations but also requires significant investment in upgrading security measures to defend against future attacks.
IV. DDOS ATTACK DETECTION TECHNIQUES
A. Traffic Analysis
Traffic analysis is one of the foundational methods for detecting DDoS attacks. By analyzing incoming network traffic, anomalies such as high traffic volume from a small number of IP addresses or traffic with suspicious patterns can be identified. This method relies on predefined traffic baseline metrics for comparison.
B. Signature-Based Detection
This technique involves identifying known attack patterns using predefined signatures. While effective in detecting known attacks, this method is less effective against new or evolving attack techniques that have not been previously cataloged.
C. Machine Learning and AI-Based Detection
With the rise of sophisticated DDoS attacks, machine learning and artificial intelligence have shown promise in detecting novel attack patterns. Algorithms can be trained on large datasets of network traffic to identify anomalies that deviate from normal traffic behavior. This proactive detection is more adaptive and effective in real-time monitoring.

Fig. 3 Machine Learning-Based DDoS Detection
Here is the diagram illustrating machine learning-based DDoS detection, showing how network traffic is analyzed in real-time to identify anomalies.
V. MITIGATION STRATEGIES
A. Traditional Mitigation Methods
- Rate Limiting: Limiting the number of requests a client can make to a server within a specific time frame can mitigate the impact of DDoS attacks.
- Blackhole Routing: This involves rerouting traffic to a "black hole" where it is discarded to prevent overload on the target system.
- Traffic Filtering: Filters can be applied to distinguish between legitimate and malicious traffic, blocking attack traffic while allowing normal traffic to pass through.
B. Traffic Analysis
- Cloud-Based DDoS Protection: Services such as Cloudflare and Akamai provide scalable DDoS protection by redirecting traffic through their cloud infrastructure, where malicious traffic can be scrubbed before reaching the target.
- Content Delivery Networks (CDNs): CDNs distribute traffic across a network of servers, helping to absorb high volumes of traffic and mitigate DDoS attacks.
C. Hybrid Solutions
Combining traditional and modern techniques, hybrid DDoS protection strategies ensure that attacks are mitigated at both the network level and through application-level filtering.
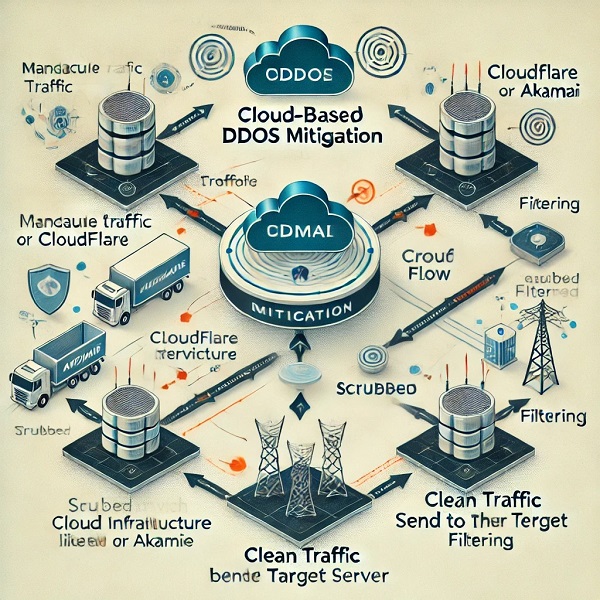
Fig. 4 Cloud-Based DDoS Mitigation
Here is the diagram illustrating cloud-based DDoS mitigation, showing how malicious traffic is filtered through a cloud service like Cloudflare or Akamai before reaching the target.
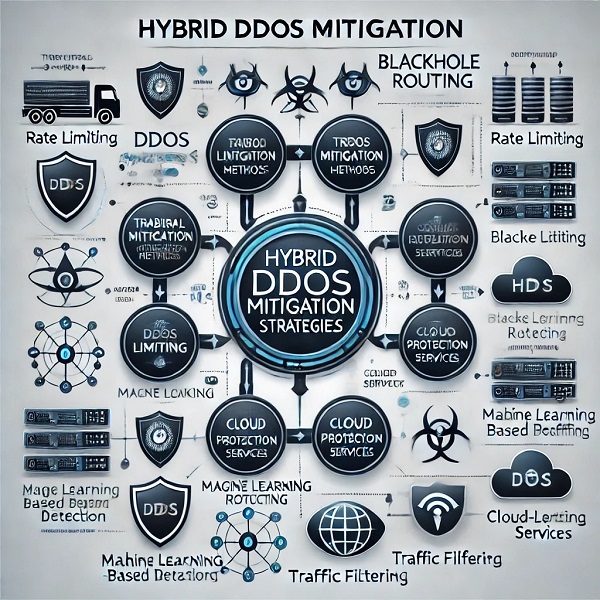
Fig. 5 Hybrid DDoS Mitigation Strategies
This diagram shows how traditional mitigation techniques (like rate limiting, blackhole routing) are integrated with modern approaches (such as machine learning-based detection and cloud-based protection)

Fig. 6 IoT Device Security for DDoS Prevention
This diagram illustrates how securing IoT devices—through strong authentication, firmware updates, and intrusion detection—can help prevent them from becoming part of a botnet used in DDoS attacks.
VI. CASE STUDY: THE 2016 DYN DDOS ATTACK
One of the most significant DDoS attacks occurred in October 2016 when the Dyn DNS service was targeted. The attack, utilizing the Mirai botnet, disrupted major websites, including Twitter, Spotify, and Reddit. This attack involved the use of IoT devices like cameras and routers, which were hijacked and used as part of a massive botnet. The incident highlights the growing threat of IoT-based DDoS attacks and the vulnerabilities inherent in connected devices.
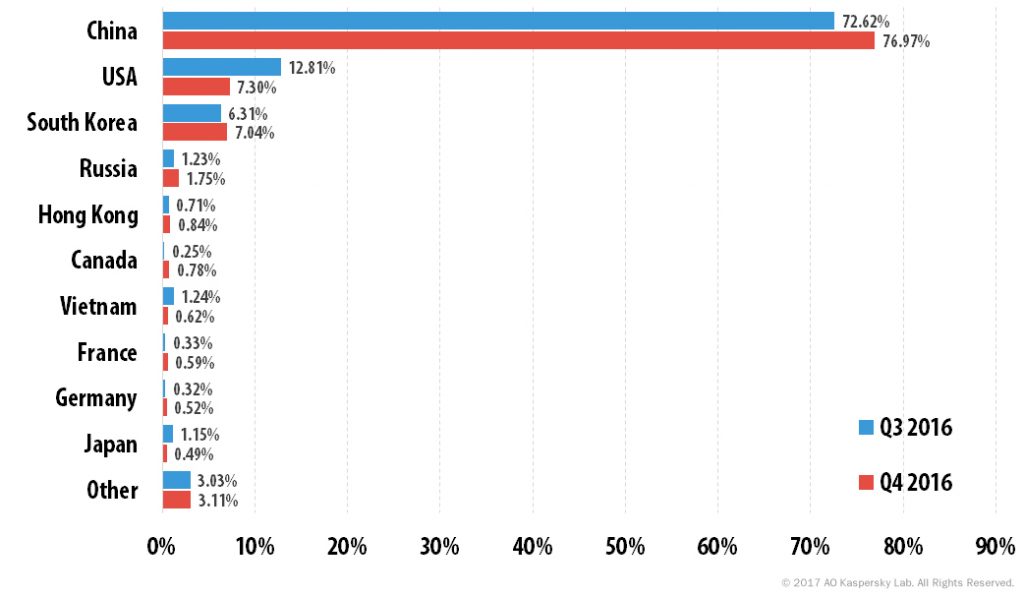 Fig. 7 Distribution of DDoS attacks by country
Fig. 7 Distribution of DDoS attacks by country
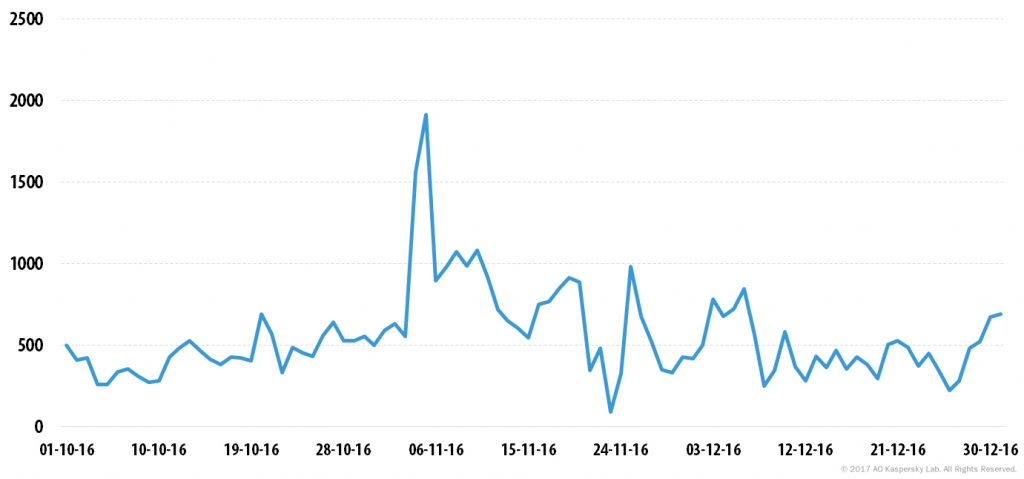 Fig. 8 Number of DDoS attacks over time in Q4 2016
Fig. 8 Number of DDoS attacks over time in Q4 2016
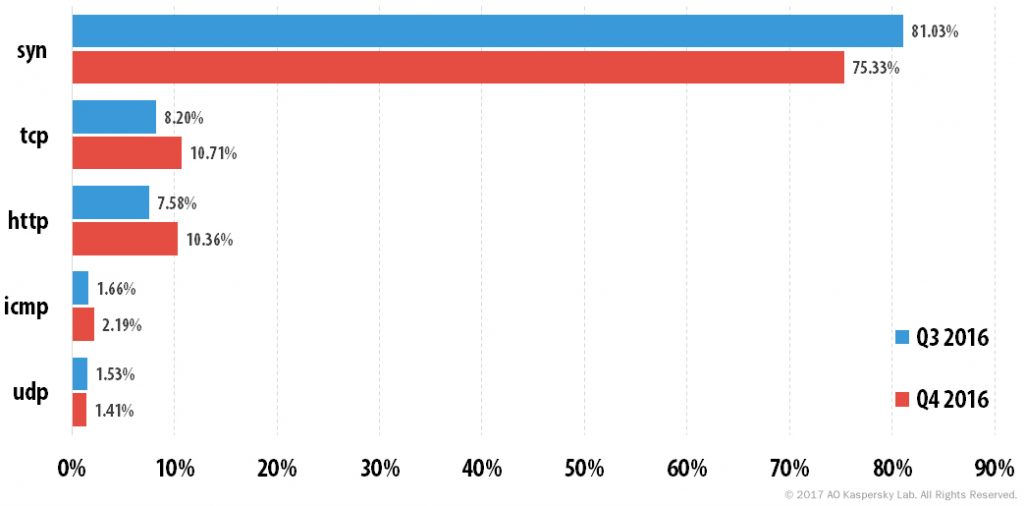 Fig. 9 Distribution of DDoS attacks by type, Q3 and Q4 2016
Fig. 9 Distribution of DDoS attacks by type, Q3 and Q4 2016
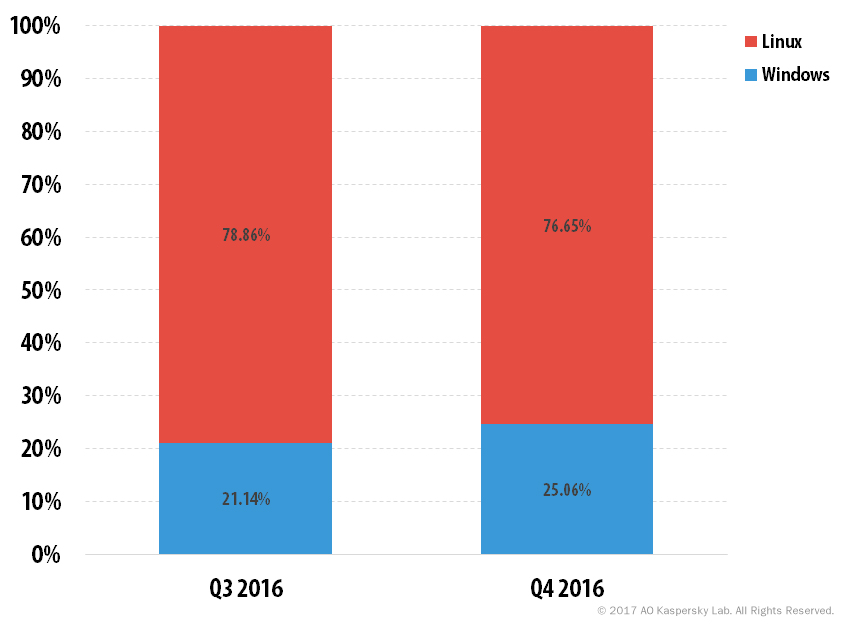
Fig. 10 Correlation between attacks launched from Windows and Linux botnets
VII. FUTURE DIRECTIONS
A. The Role of Blockchain in DDoS Mitigation
Blockchain technology offers promising avenues for securing the network infrastructure by decentralizing control and verifying data integrity. Smart contracts and blockchain's immutability may assist in mitigating DDoS attacks by providing an immutable log of attack data and by decentralizing response mechanisms.
B. The Growing Role of Artificial Intelligence
AI-driven predictive models and deep learning can play a key role in improving the proactive defense of systems against DDoS attacks. These models can learn from historical attack data and adapt to detect new patterns in real-time.
C. IoT Security and DDoS Prevention
As IoT devices become ubiquitous, their role in facilitating DDoS attacks grows. Future research will need to focus on securing these devices, including better authentication mechanisms and anomaly detection systems at the device level.
Conclusion
DDoS attacks continue to evolve, posing a serious threat to online businesses and critical infrastructure. While traditional methods of mitigation remain relevant, the adoption of advanced technologies like machine learning, cloud services, and blockchain may provide more robust solutions. By continuously improving detection and mitigation strategies, organizations can better protect themselves against the growing threat of DDoS attacks. Future research must focus on enhancing the scalability of defenses and addressing the vulnerabilities of IoT devices, which are increasingly being exploited as part of DDoS botnets.
References
[1] Tabriz, D., & Hosseini, S. (2021). An overview of DDoS attack detection and mitigation techniques. International Journal of Computer Applications, 32(7), 42-58. [2] Ponemon Institute. (2019). Cost of DDoS Attacks. https://www.ponemon.org [3] DDoS Protection Services – Cloudflare. (2020). Comprehensive DDoS Mitigation. https://www.cloudflare.com [4] Vacca, J. R. (2017). Computer and Information Security Handbook. Elsevier. [5] Chong, K., & Lee, B. (2020). A Machine Learning Approach for DDoS Attack Detection in IoT Networks. Journal of Computer Networks and Communications, 2020, Article ID 1251947. [6] Mishra, P., & Hwang, M. (2019). Botnet Detection and Mitigation in Cloud-Based Environments. International Journal of Computer Science and Information Security (IJCSIS), 17(1), 9-16. [7] Liu, Y., & Liu, J. (2018). Mitigating DDoS Attacks with Traffic Analysis and AI Techniques. Future Internet, 10(2), 15. [8] Nash, K., & MacDonald, P. (2021). Distributed Denial of Service Attacks: A Modern Approach to Detection and Prevention. IEEE Transactions on Network and Service Management, 18(2), 1981-1993. [9] Alves, S., & Sousa, P. (2020). Cloud-Based DDoS Mitigation Techniques: A Survey. Journal of Cloud Computing: Advances, Systems, and Applications, 9(1), 1-15. [10] Lee, S., & Kim, H. (2021). Hybrid Approaches to DDoS Detection and Mitigation. Journal of Cybersecurity, 7(4), 89-101. [11] Hussain, F., & Ahmed, E. (2021). DDoS Detection Using Machine Learning Algorithms: A Review. International Journal of Computer Applications, 174(6), 22-29. [12] Bashir, A., & Al-Fuqaha, A. (2020). An Intelligent DDoS Attack Detection Framework for Cloud-Based Applications. IEEE Transactions on Cloud Computing, 8(6), 1465-1476. [13] Xiao, L., & Li, H. (2019). Application of AI in DDoS Attack Detection: A Survey. Computers, 8(3), 29. [14] Gao, Z., & Zhang, X. (2020). Anomaly-Based DDoS Detection Using Machine Learning: A Comparative Study. Journal of Information Security, 11(2), 15-23. [15] Akamai Technologies. (2021). State of the Internet/Security: DDoS Attack Trends and Insights. https://www.akamai.com [16] Cisco. (2021). DDoS Threats: Protecting Your Network from Emerging DDoS Risks. https://www.cisco.com [17] Radware. (2021). 2016-2021 Global DDoS Threat Landscape Report. https://www.radware.com [18] Cloudflare. (2020). Comprehensive DDoS Mitigation: Protecting Your Applications. https://www.cloudflare.com [19] Imperva. (2020). Global DDoS Threat Landscape Report: Trends, Threats, and Mitigation Strategies. https://www.imperva.com
Copyright
Copyright © 2025 Syed Ali Nawaz Zaidi, Jianping Li, Yubo Tan. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.

Download Paper
Paper Id : IJRASET66669
Publish Date : 2025-01-24
ISSN : 2321-9653
Publisher Name : IJRASET
DOI Link : Click Here
 Submit Paper Online
Submit Paper Online

